TCP Proxy
The TCP Proxy plugin serves as an essential tool for inspecting data exchanged between two TCP nodes. Functioning as a man-in-the-middle, it offers a seamless way to monitor and log TCP communication, addressing common limitations encountered with traditional sniffing tools like the Pcap Sniffer plugin.
Basic Setup
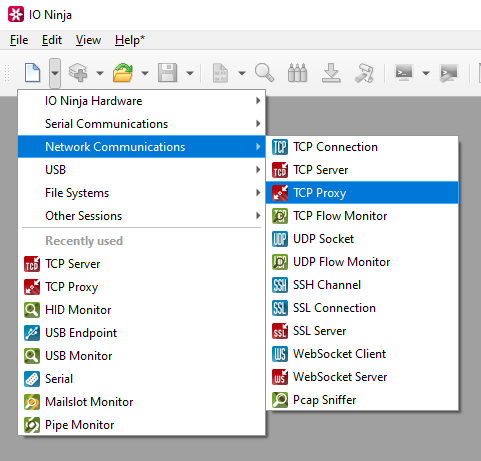
In IO Ninja, click the “New Session” dropdown and select “TCP Proxy”.
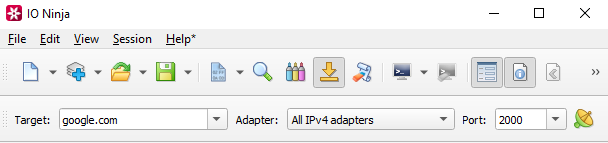
Set the target address, adapter and port.
Note
For example, if you wanted to route IPv4 traffic on port 2000 to example.com, then you would set the target address to “example.com”, the adapter to “All IPv4 adapters” and the port to “2000”.
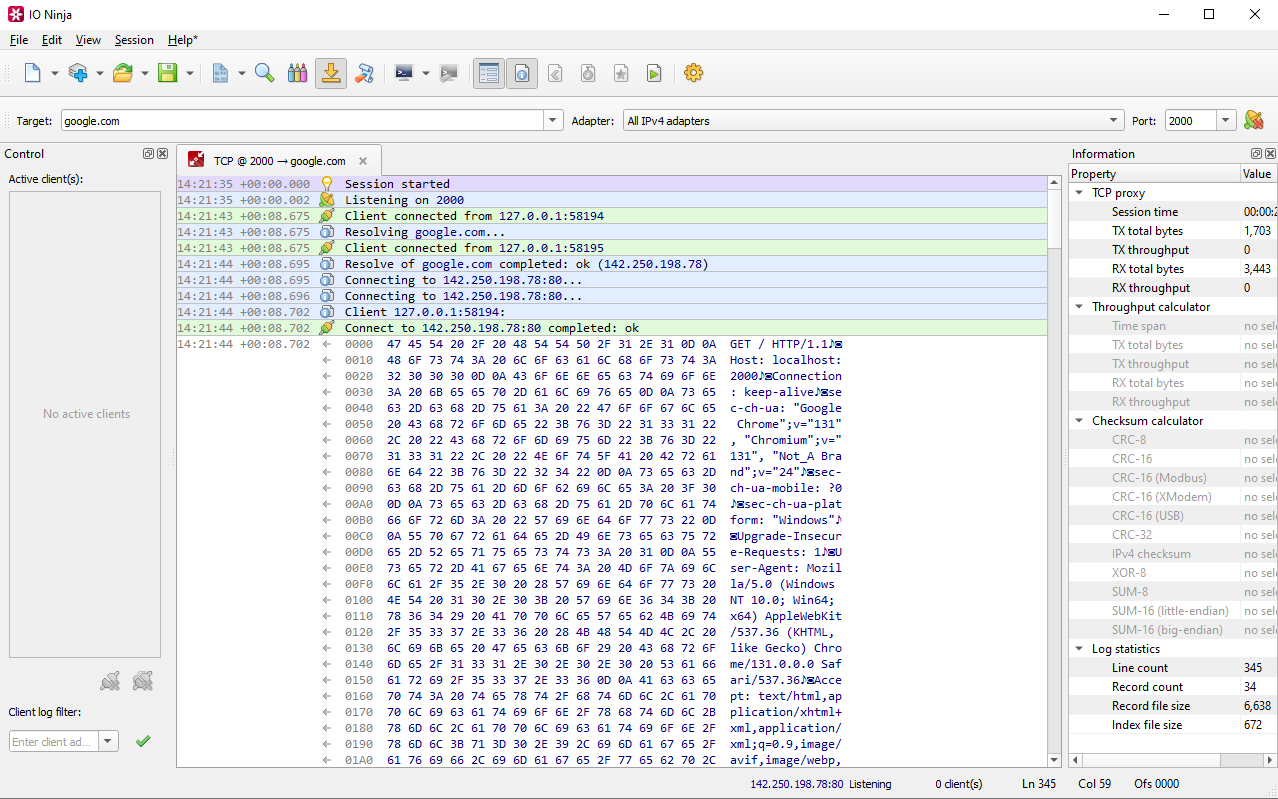
Click the “Listen” button to start intercepting traffic.

After initating connections to the proxy, intercepted traffic will show in the TCP Proxy window.
Adjust settings as needed via the “Settings” button (see “Settings” section below for details).
Settings

Setting |
Description |
Default |
|---|---|---|
Adapter |
Local network adapter to bind to. Pick one from the list of installed network adapters (or bind to all installed |
All IPv4 adapters |
Local port |
Local port to bind to. Setting this to |
8080 |
Reuse address |
Allow multiple sockets to share the same local address. Maps to the |
False |
Remote address |
Remote address to connect to. Can be specified via IPv4 ( |
|
Remote port (default) |
Remote port to connect to in cases when a port is not explicitly specified in Remote address. |
80 |
TCP Nagle algorithm |
Delay transmission to reduce the number of small |
False |
TCP reset |
Drop TCP connections abruptly with a |
False |
TCP keep-alives |
Detect connection loss with |
False |
Read parallelism
(Windows-only)
|
Maximum number of read requests to issue in parallel. Having more than one pending read at a time helps with increasing read throughput when incoming data arrives in rapid streams (after filling one user buffer, the kernel can immediately switch to the next one without any waiting). Increasing this number beyond 4 usually won’t yield any extra performance gains. |
4 |
Read block size (B) |
The size of each individual read block submitted to the underlying transport. |
4KB |
RX buffer size (B) |
The full size of the incoming data ( |
16KB |
TX buffer size (B) |
The full size of the outbound data ( |
16KB |
Keep read block size |
Don’t merge read blocks in RX buffer. Incoming data blocks coming in quick succession can be merged together so that IO Ninja writes them to log as a whole. When this option is set to |
False |
Keep write block size |
Don’t merge write blocks in |
False |
RX buffer full notifications |
Toggle warnings in log about the incoming data ( |
False |
Note
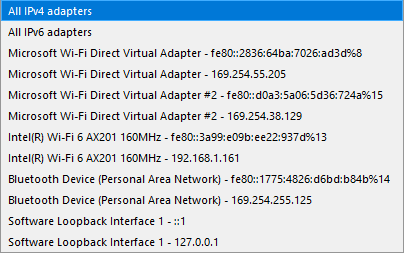
An example of an adapter dropdown on a typical Windows laptop is shown below: